A small click of the mouse can have big potential consequences. Are you reporting this?






You start your workday unsuspectingly. Your computer indicates that an update needs to be installed. After rebooting, a video link from an unknown source suddenly appears on your screen. A dark voice speaks to you: PhantomX. The atmosphere of your desktop changes abruptly. Welcome to the team of cybercriminals. Your system has been taken hostage. All you can do is listen to regain control of your system.
You find yourself face to face with PhantomX. He explains that you have just fallen for one of his tricks. But you get a chance. Together with him, you will explore the world of cybercrime. Namely, he wants you to perform a hack on your own company. Only then will you regain control of your systems. The introduction includes:
You have just been hacked by PhantomX. Together with him, you take on the ultimate challenge: hacking your company and colleagues. But first you have to get onto the web completely anonymously. Using a VPN connection, you make sure your IP address is masked. With PhantomX's help, you then anonymously execute his cunning plan.
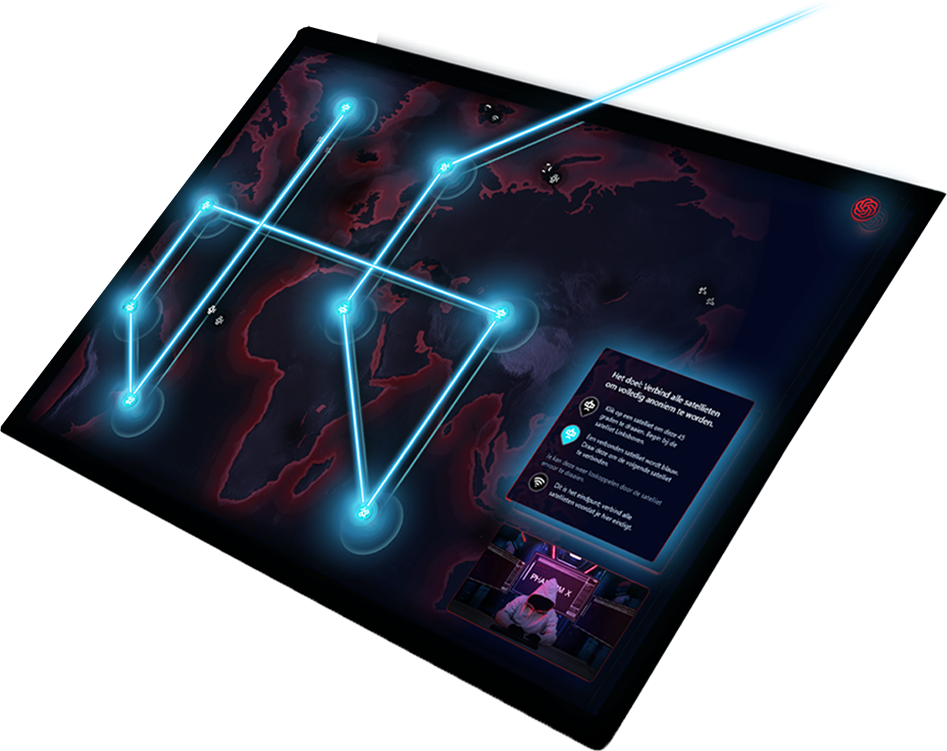
You will create connections through the program in order to hide your IP address. This will cover the following topics:
Do you have what it takes to become a real hacker? Discover all the levels and get to know the different subjects of the Cyber Kill Chain.